Doing It Right The First Time
Mark Ridgeway • November 10, 2017
Have questions? Let's talk!
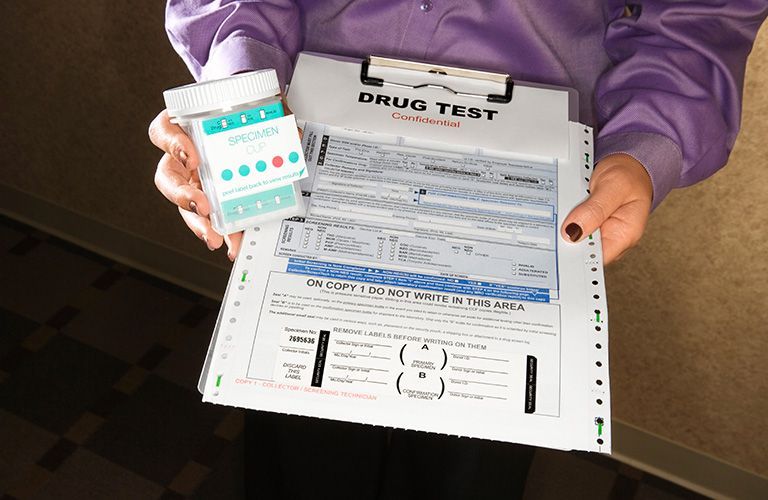
Drug testing in the workplace is a practice that has gained significant attention in recent years. It involves screening employees for the use of illicit substances and, in some cases, the abuse of prescription medications. While there are arguments against workplace drug testing, it undeniably offers numerous benefits to both employers and employees. In this blog post, we will explore the advantages of employee drug testing programs and why you should implement one for your business. Safety and Productivity One of the most compelling reasons for drug testing in the workplace is the enhancement of safety and productivity. Employees under the influence of drugs or alcohol are more likely to cause accidents, make errors, and exhibit impaired judgment. Drug testing helps identify individuals with substance abuse issues, preventing them from putting themselves and their colleagues at risk. A safer workplace leads to increased productivity, as employees can focus on their tasks without worrying about the consequences of impaired coworkers. Legal Compliance Many industries and government contracts require drug testing as part of compliance with specific regulations. By implementing drug testing, employers can ensure they meet these legal requirements, avoiding potential fines or the loss of contracts. This legal compliance also extends to workers' compensation claims, where having a drug-free workplace can be essential in demonstrating that accidents were not caused by substance abuse. Reduction of Healthcare Costs Drug testing can contribute to reducing healthcare costs. Employees struggling with substance abuse issues often require more medical attention due to the health problems associated with drug and alcohol use. Identifying these individuals early on and offering support and treatment can lead to healthier employees, lower healthcare expenses, and a reduced burden on insurance premiums. Reduce Legal Liability The U.S. Department of Labor estimates that drug use by employees cost businesses billions of dollars annually as a result of workplace accidents. The implementation of a drug testing policy can assist your business in reducing these costs by lowering your risks and liability. Improved Employee Morale A workplace free from substance abuse concerns can boost employee morale. When employees know their colleagues are not abusing drugs or alcohol, they are more likely to feel safe, respected, and motivated. This can lead to increased job satisfaction and a more positive work environment, ultimately reducing turnover rates. Enhanced Company Reputation Employers that invest in drug testing programs demonstrate a commitment to a safe and responsible workplace. This commitment can enhance a company's reputation, making it more attractive to potential employees, customers, and partners. A strong reputation for maintaining a drug-free environment can differentiate a company in a competitive marketplace. Early Intervention Drug testing not only identifies employees with substance abuse issues but also offers an opportunity for early intervention. Employers can connect these individuals with resources, such as Employee Assistance Programs (EAPs), counseling, and treatment options. Early intervention can prevent the escalation of substance abuse problems and help employees overcome their issues, ultimately preserving their careers. Deterrence The knowledge that random drug testing is in place can act as a deterrent for employees who may consider using drugs or alcohol inappropriately. The fear of testing positive can discourage substance abuse and create a culture of accountability within the workplace. In conclusion, when administered fairly and with respect for employees' rights, drug testing can be a valuable tool in promoting a healthier and more prosperous workplace. Ultimately, the benefits of workplace drug testing outweigh the potential drawbacks, leading to safer, more productive, and more successful organizations. At CourtHouse Concepts, we can provide and manage pre-employment drug screening and set up random drug testing for your company. Call us today for a custom proposal!




